Remcos malware continues to pose a significant threat, as HPT’s cybersecurity experts have recently released a technical analysis of a Remcos distribution campaign that enables threat actors to silently take control of systems and exfiltrate sensitive data over extended periods. The report highlights how attack techniques are becoming increasingly sophisticated, combining multi-layered obfuscation and disguise mechanisms to bypass traditional security solutions. This trend reflects a rapidly evolving threat landscape, requiring organizations and users to proactively strengthen their defenses against increasingly difficult-to-detect cyber risks.
What is Remcos malware? Understanding the risks of Remote Access Trojans
Remcos (Remote Control and Surveillance) is a type of Remote Access Trojan (RAT) that has been widely used in cyberattack campaigns since around 2016. Initially, Remcos was developed as a legitimate remote administration tool; however, over time, it has been exploited by threat actors for malicious purposes.
In recent years, Remcos has made a strong comeback with increasingly sophisticated attack campaigns, combining phishing, fileless techniques, and the abuse of legitimate operating system tools to evade detection. With its ability to completely control infected systems, Remcos has become a serious threat to businesses and organizations.
The growing threat of Remote Access Trojans
Remote Access Trojan (RAT) campaigns continue to increase in both frequency and sophistication. Cybersecurity reports show that threat actors are increasingly leveraging legitimate tools, along with fileless execution and multi-layered obfuscation techniques, to maintain stealthy and persistent control over victim systems.
These campaigns are not only used for surveillance and data collection but also serve as a foundation for more advanced attacks such as lateral movement, privilege escalation, and the deployment of additional malware.
Through continuous threat monitoring and analysis, HPT experts have observed the resurgence of Remcos, a RAT family originally designed for legitimate remote administration but now widely abused in cyberattack campaigns. Recently, this malware has continued to evolve by incorporating phishing, fileless execution, and the abuse of built-in operating system tools to infiltrate and control victim environments.
Initial access and infection chain
According to HPT’s cybersecurity, Remcos campaigns typically begin with phishing emails disguised as financial invoices, HR-related documents, or shipping information. These emails often contain malicious attachments in common formats such as Word/Excel files with macros, ZIP archives, LNK shortcuts, or RTF files exploiting vulnerabilities.
Once the victim opens the malicious attachment, the infection chain is triggered. A .hta file invokes mshta.exe to execute embedded scripts, which then decode and launch PowerShell commands. These commands download additional malicious components from remote servers, initiating subsequent stages of the attack.
Steganography and advanced attack techniques in image files
One of the most notable techniques observed by HPT's cybersecurity is the use of image files (.png) to conceal malicious payloads. Although these files appear to be legitimate images, they actually contain encoded payload data. After being downloaded, the malware silently extracts the hidden content, performs multi-layer decoding, and executes the payload directly in memory. By avoiding writing files to disk, this technique enables the malware to bypass traditional signature-based detection mechanisms.
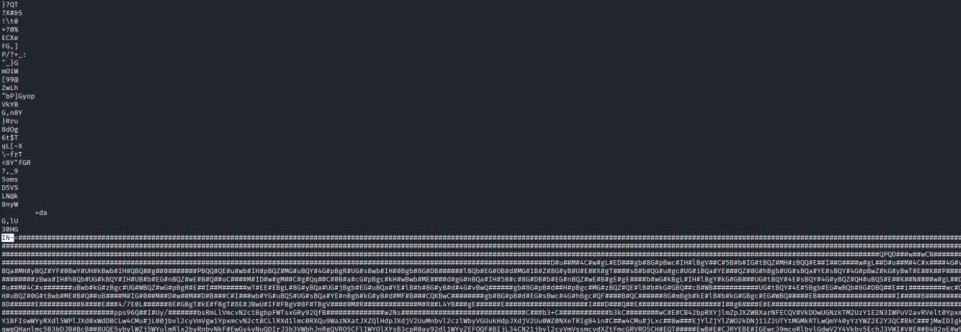
Illustration of payload hidden within an image file
HPT's cybersecurity shows that the decoded payload is loaded into memory as a .NET assembly and executed via reflection. In the final stage, the Remcos Agent is fully deployed, allowing threat actors to monitor user activity, steal sensitive data, remotely control the system, and maintain long-term persistence.
In addition, the malware can establish persistence mechanisms, evade sandbox environments, and utilize dynamic DNS infrastructure for Command and Control (C2) communication, significantly enhancing its stealth and persistence capabilities.
Indicators and potential risks
During attack reconstruction, HPT's cybersecurity observed notable indicators such as the presence of the Caspol.exe process and abnormal connections to remote infrastructure. However, due to fileless execution and multi-layer obfuscation, most malicious activities remain stealthy, making detection extremely challenging using conventional methods.
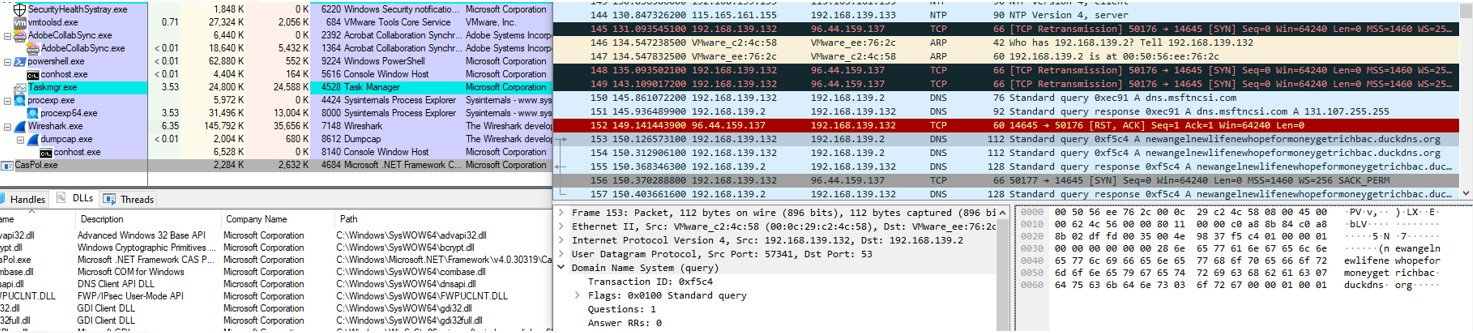
Caspol.exe process and DNS query activitySecurity recommendations from HPT experts
In response to increasingly sophisticated cyber threats, HPT recommends that organizations and users proactively strengthen their security posture:
- Enhance cybersecurity awareness
- Closely monitor script-based activities (HTA, PowerShell, mshta.exe)
- Detect anomalies in network traffic and dynamic DNS queries
- Deploy sandbox environments combined with EDR/XDR capable of analyzing memory injection and steganography
- Apply zero-trust principles and restrict execution of untrusted macros/scripts
Comprehensive defensive solutions from HPT
To proactively protect enterprises against increasingly sophisticated cyber threats, HPT delivers a portfolio of specialized cybersecurity solutions and services tailored to modern thre at landscapes:
- Penetration Testing Services: Simulated real-world attacks designed to identify weaknesses across the organization’s attack surface before adversaries can exploit them.
- 24x7 Security Operations Center (SOC) Monitoring: Continuous monitoring to detect, analyze, and respond to suspicious activities across servers and end-user endpoints in real time.
- Cybersecurity Consulting Services: Development of resilient backup strategies following the 3-2-1 rule, combined with incident response and recovery drills to ensure data availability and business continuity.
- User Awareness Assessment & Training (Email Phishing): Strengthening the “human firewall”, the organization’s most critical line.